Azure B2C has the capability to manage custom user attributes. Those attributes are custom extension on the Azure AD profile in the background. But how do they work and how can you access them with the Graph API?
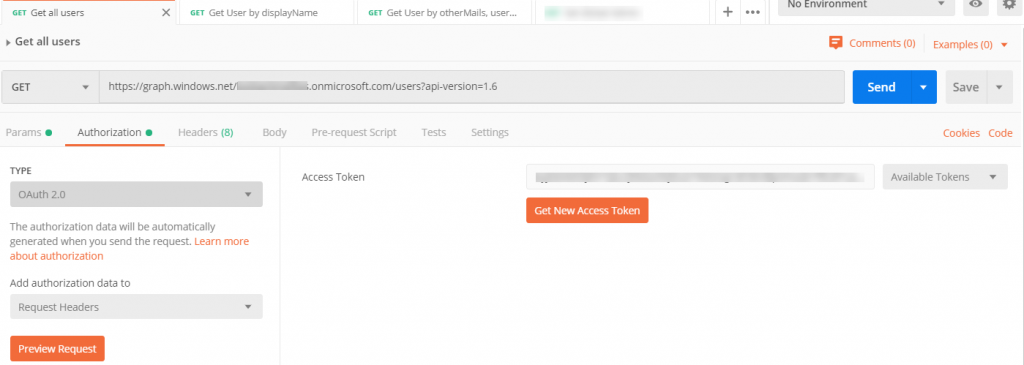
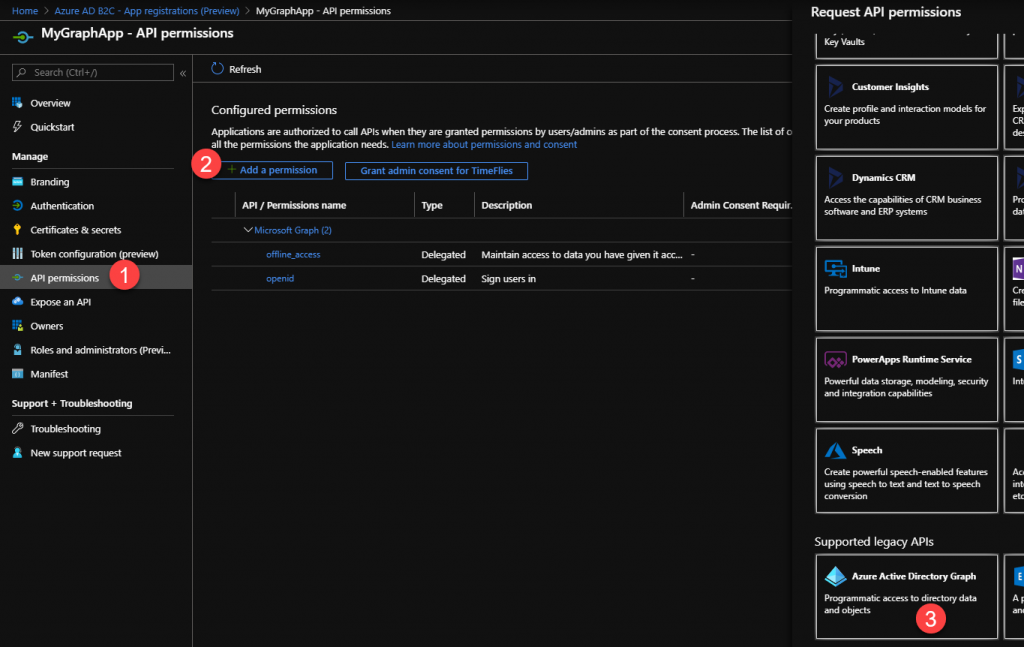
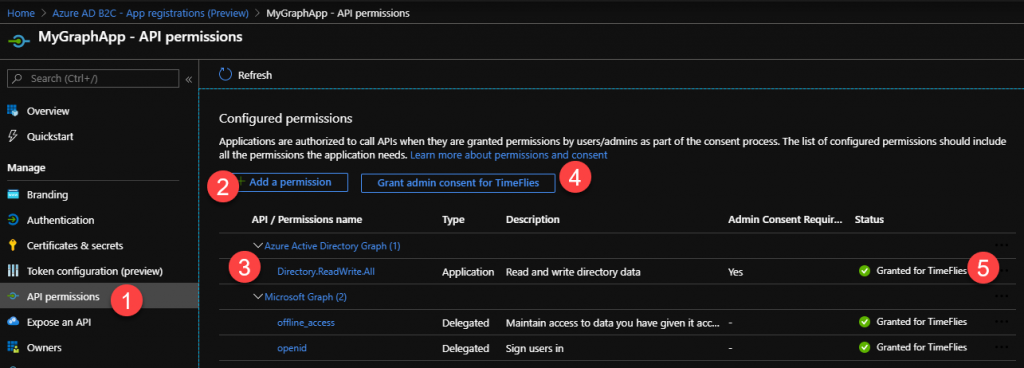
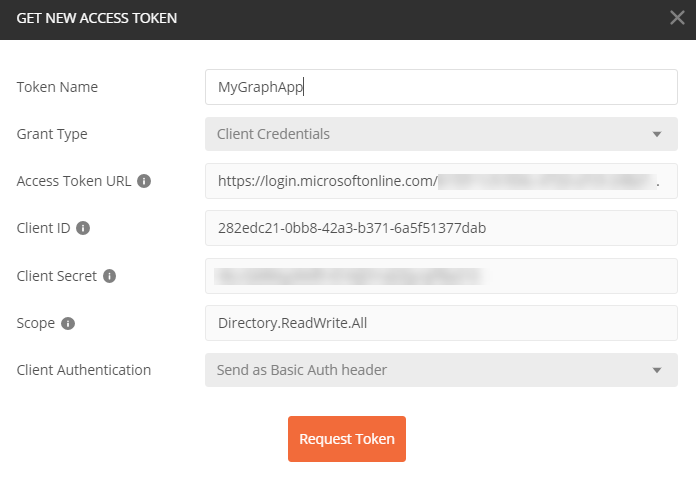
Accesstoken
First you need an accesstoken. The get an access token, read my previous post with an introduction to Azure B2C with the Graph API or how to find users in Azure B2C with the Graph API.
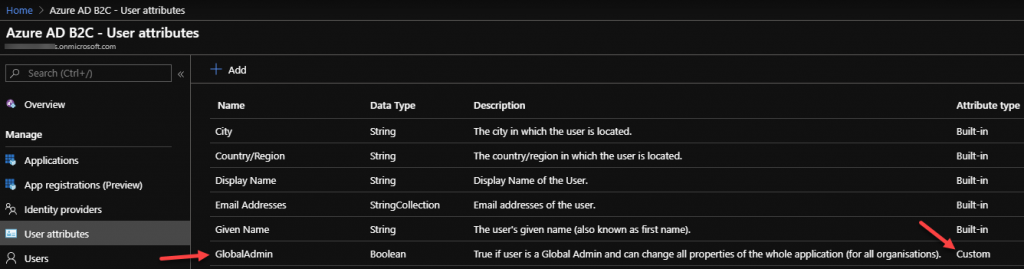
Create a Custom User Attribute
In this sample, we are going to create a custom attribute called “GlobalAdmin”. It’s just a boolean for simplicity.
You can get the details of the user with the ObjectId using the url:
https://graph.windows.net/{{tenant}}.onmicrosoft.com/users/fdabad31-92bf-43f7-8370-53c280ef042b?api-version=1.6
When the attribute is new, you won’t find the attribute on the user. Not even with the default value (in our case false because of the boolean).
Set a Custom User Attribute
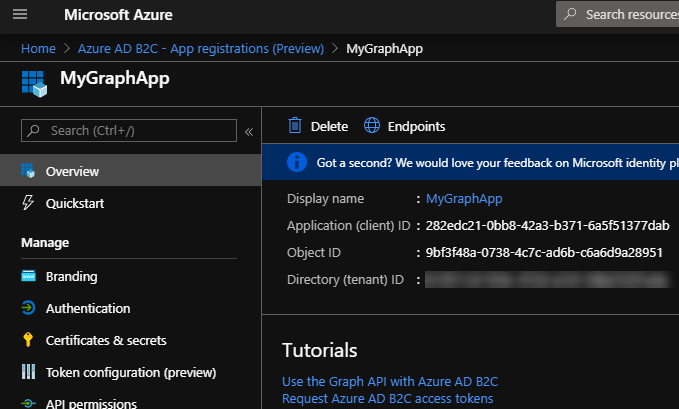
To set the custom created user attribute we need to know where the custom attribute is coming from. An B2C user attribute is an extension to the Azure AD. Just as you would do with the regular Azure AD. You can imagine that if there is a big Azure AD and there are many applications connected to it. So Microsoft decided that an extension belongs to an application.
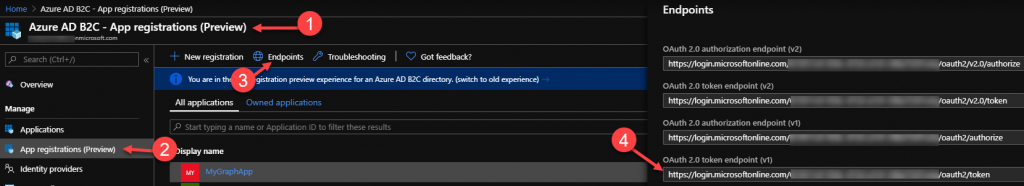
In our case, B2C it self is an application on top of the Azure AD. So Azure B2C has an application (app registration) in your Azure AD tenant. You can see this, when you navigate to the Azure AD blade in the Azure portal and go to the app registrations. When you click on the “All applications” you will see the default “b2c-extensions-app” application. You can also navigate to new preview blade in B2C it self.
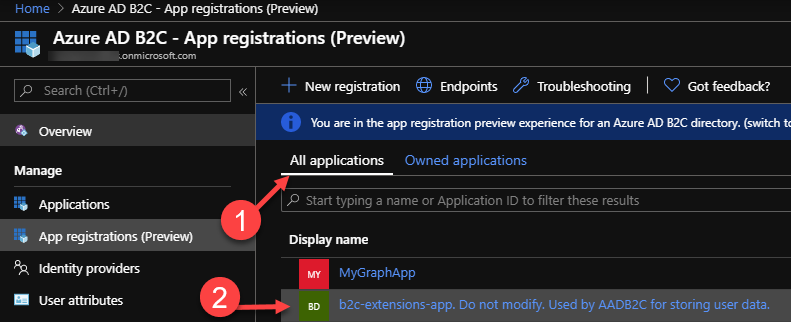
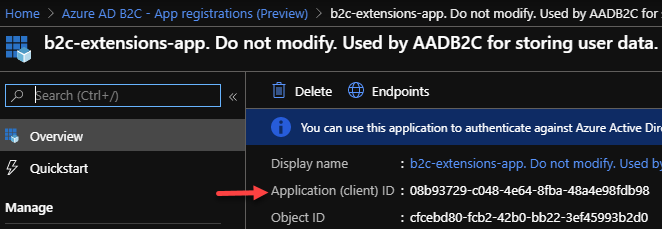
You need the “ApplicationId” (ClientId) of that “b2c-extensions-app”. So open it, and copy it. Do not change anything on this application otherwise your Azure B2C can be broken!
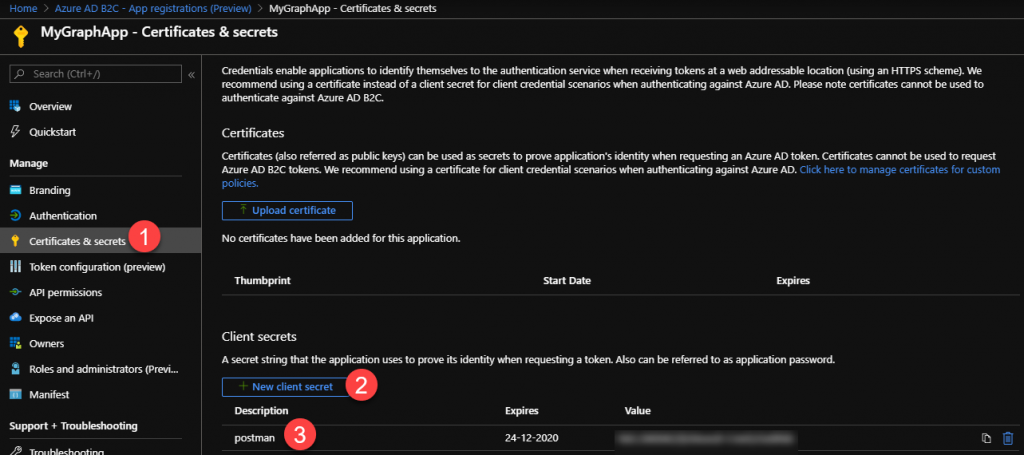
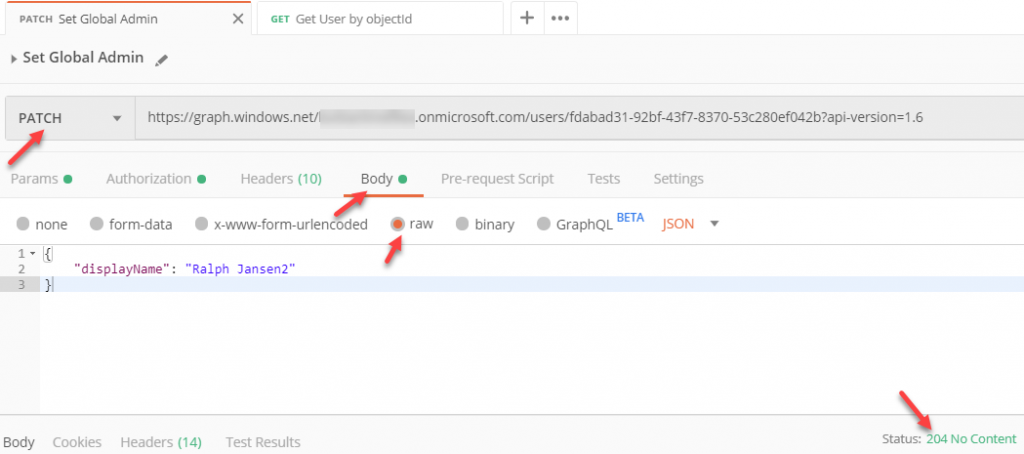
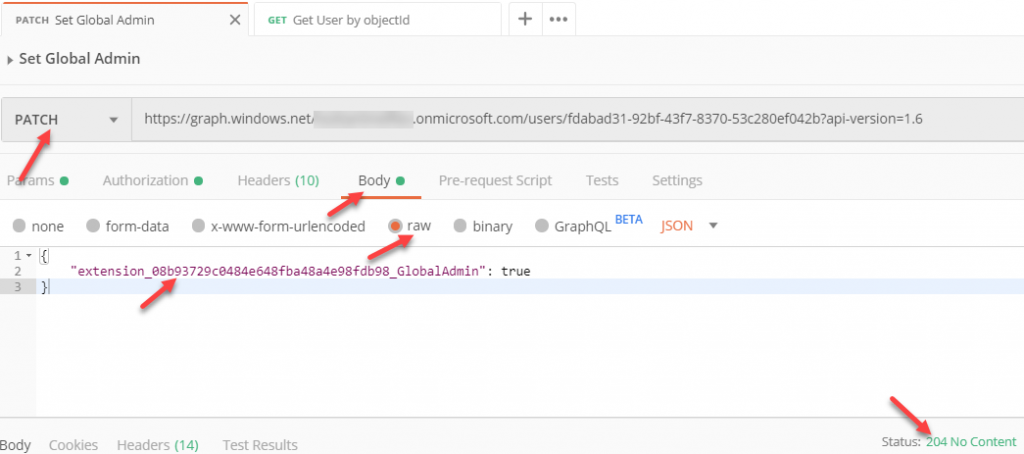
We have all the information that we need, so let’s set the custom attribute. Create a new postman request and use the same url as getting the user detail information with the ObjectId. Set the type of request to “Patch” and add a header “Content-Type” with the value “application/json”.
But in the body the fields (attributes) you want to set. Let’t practice with the “displayName” of the user using the following body:
{
"displayName": "Ralph Jansen2"
}
Hit send and the return code will be a 204 No Content. When you get the user, you will see the updated value. It can take about 15 seconds before the update is propagated over the whole world.
Now that is working, let’s update the custom user attribute “GlobalAdmin”. The attribute belongs to an application. In our case the applicationid is “08b93729-c048-4e64-8fba-48a4e98fdb98”. An Azure B2C user attribute extension will have the syntax “extension_b2cApplicationIdWithoutDashes_attributeName”. So this will result in “extension_08b93729c0484e648fba48a4e98fdb98_GlobalAdmin” in our case. So let’s put it in the body with the value true (because our attribute is a boolean) and hit send.
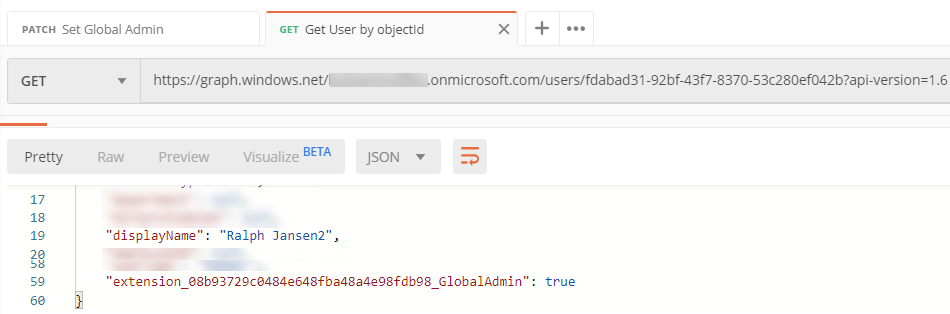
Get a Custom User Attribute
Let’s see the result by getting the user details again with the ObjectId. You will see the new attribute on the user (can take again a few seconds).